How to Spot Fake Dating Profiles in 2026
Tips for finding out if someone is fake on dating apps
The digital dating landscape has undergone a massive transformation. While apps like Tinder, Bumble, and Hinge have made finding a partner more accessible, they have also become a playground for sophisticated scammers. In 2026, the rise of high-fidelity AI-generated images and advanced large language models (LLMs) has made “catfishing” more difficult to detect than ever before.
Identifying a fake profile is no longer just about looking for grainy photos or bad grammar. It requires a modern understanding of digital footprints, psychological triggers, and technical verification tools. This guide will walk you through the advanced techniques to protect your heart, your data, and your bank account from online imposters.
1. The Evolution of the “Catfish” in the Age of AI

Years ago, a fake profile was easy to spot: one or two photos of a model, a bio full of typos, and a request for money within the first hour. Today, scammers use AI to create incredibly realistic personas.
AI-Generated Faces and Deepfakes
In 2026, scammers use tools like “Generative Adversarial Networks” (GANs) to create faces of people who do not actually exist. These photos look perfect—perfect lighting, natural skin textures, and realistic backgrounds. However, AI often struggles with asymmetrical details like earrings, glasses, or the way hair meets the background.
Sophisticated Chatbots
With advanced AI, a scammer doesn’t even need to be online to talk to you. They use automated scripts that can carry on a convincing conversation for days, building trust before a human ever takes over the keyboard to execute the scam.
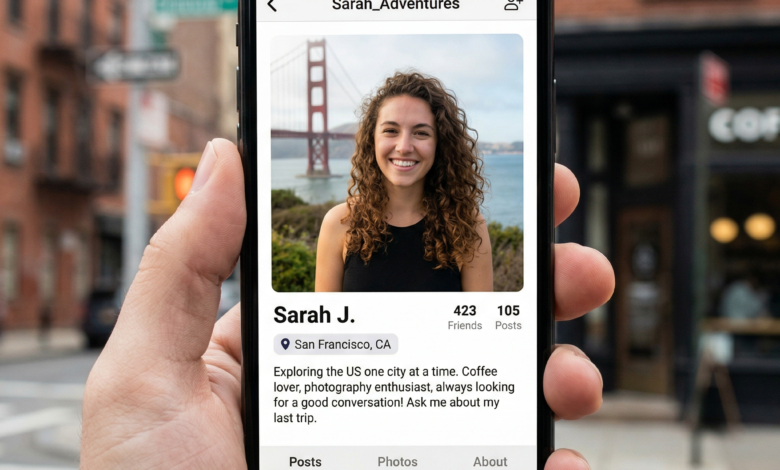
2. Technical Red Flags: How to Analyze a Profile Like a Pro
Before you send that first message, take a deep dive into the profile itself. Professional scammers often leave breadcrumbs that the average user misses.
The “Too Perfect” Aesthetic
If every photo looks like it was taken for a high-end fashion magazine or a professional travel blog, be wary. While many people have great cameras, a genuine profile usually includes at least one “candid” shot—a blurry selfie with friends, a mirror pic with messy background details, or a photo with a pet.
Analyzing the Metadata of a Persona
Look at the consistency of the photos. Does the person look the same age in every shot? Is the weather consistent with the supposed location? If they claim to be in New York City in January but are wearing a t-shirt in a sunny park in every photo, something is wrong.
The Lack of Social Integration
Most major dating apps allow users to link their Instagram or Spotify. If a profile is “bare bones” with no linked accounts, it’s a yellow flag. In 2026, having a “zero-width” digital footprint is rare for the demographic typically using dating apps.
3. Psychological Tactics Used by Modern Scammers
Scammers don’t just steal photos; they steal emotions. They use specific psychological triggers to lower your defenses.
The “Hero” or “Victim” Narrative
Scammers often adopt personas that evoke immediate respect or sympathy. Common “Hero” tropes include military personnel stationed overseas, doctors working for international NGOs, or successful “self-made” crypto investors. “Victim” tropes involve tragic backstories about deceased spouses or being “trapped” in a foreign country due to a business legalities.
Love Bombing and False Urgency
If someone starts using terms of endearment (like “soulmate” or “my love”) within 24 hours of matching, you are being “love bombed.” This is a tactic designed to create an intense emotional bond quickly. Once the bond is formed, they introduce a “crisis” that requires your financial help.
Isolation from the Platform
A massive red flag is the immediate request to move the conversation to an encrypted app like WhatsApp, Telegram, or Signal. They do this because dating apps have automated safety filters that flag words like “bank,” “transfer,” or “crypto.” By moving you off-platform, they escape the app’s security net.
4. How to Use Reverse Image Search and Verification Tools

If your “gut feeling” is tingling, it’s time to use the technical tools available to verify their identity.
Google Lens and TinEye
Take a screenshot of their main profile photo and upload it to Google Lens or TinEye. If that photo appears on a stock photography site, a Pinterest board, or someone else’s famous Instagram account, you’ve found a fake.
Searching the Bio Text
Scammers are often lazy. They copy and paste “deep” or “romantic” bios from websites. Copy a unique sentence from their bio and paste it into a search engine in quotation marks. If you find the exact same bio on a “Scam Awareness” forum, you’ve saved yourself a lot of trouble.
The Power of Social Media Cross-Referencing
If they give you their name, search for them on LinkedIn or Facebook. In 2026, most professionals have a LinkedIn presence. If they claim to be a high-flying executive but have no professional digital footprint, they are likely a “ghost” created for the scam.
5. The Golden Rule: The Video Call Test
In 2026, there is no excuse for avoiding a video call. Smartphones are universal, and every major dating app has a built-in video chat feature.
Why It’s the Ultimate Verification
A scammer using stolen photos cannot show up on a live video call. If they do use “Deepfake” technology to simulate a face, the video often looks “glitchy” or has a slight lag when they move their head quickly.
Common Excuses to Avoid Video
-
“My camera is broken.”
-
“I’m in a high-security area (military/hospital).”
-
“I have a poor internet connection.”
-
“I’m too shy for video.”
If you haven’t seen their face live after three days of talking, stop communicating. A real person who is interested in you will want to see your face and show you theirs.
6. Identifying the Most Dangerous Scams of 2026
Knowing the goal of the fake profile can help you spot the warning signs earlier.
Pig Butchering (Crypto Scams)
This is the most prevalent scam in 2026. The scammer builds a romantic connection over weeks. Eventually, they “casually” mention how much money they are making in a new crypto platform or investment app. They offer to “teach” you. They will even let you withdraw a small amount of “profit” initially to build trust. Once you deposit a large sum, the site disappears, and the “partner” ghosts you.
The “Emergency” Wire Transfer
This is the classic romance scam. They are “stuck” at an airport, need “surgery” for a child, or have their “accounts frozen” by a corrupt government. They ask for a small amount via a non-traceable method like a wire transfer or gift cards.
Sextortion and Blackmail
The scammer encourages you to send explicit photos or videos. Once they have them, they reveal their true identity and threaten to send the images to your family, friends, or employer unless you pay a “silence fee.”
7. App-Specific Security Features You Should Be Using
Modern apps have built-in tools to help you filter out the fakes. Make sure you are utilizing them to their full potential.
-
Verified Profiles Only: Set your filters to only show you users who have completed the “Selfie Verification” or “ID Verification” process.
-
Report, Don’t Just Unmatch: If you find a fake, don’t just delete the conversation. Report the profile. Most apps use machine learning to identify patterns in reported profiles to preemptively ban similar accounts.
-
Privacy Settings: Limit the amount of personal information visible on your profile until you have matched and verified someone. Avoid photos that show your home address, your car’s license plate, or your children’s school uniforms.
8. What to Do if You’ve Been Scammed
If you realize you’ve been talking to a fake, or worse, if you’ve sent money or personal information, don’t let embarrassment stop you from taking action.
-
Cease All Contact: Block them on every platform immediately. Do not explain why; just cut the line.
-
Document Everything: Take screenshots of the profile, the conversations, and any financial transactions.
-
Report to Authorities: In the United States, report the incident to the FBI’s Internet Crime Complaint Center (IC3).
-
Notify the Dating App: Alert the platform so they can take down the profile and warn other users who may have matched with them.
-
Secure Your Accounts: If you shared passwords or sensitive data, change your credentials and set up Two-Factor Authentication (2FA) on all your accounts.
9. Trust Your Instincts in a Digital World
The most powerful tool in your security arsenal is your intuition. If a match feels “too good to be true,” it almost certainly is. A person who is genuinely looking for love will respect your boundaries, answer your questions, and won’t mind proving they are who they say they are.
By combining a healthy level of skepticism with the technical verification steps outlined in this guide, you can navigate the 2026 dating world with confidence. Your safety—physical, emotional, and financial—is always more important than a potential match. Stay vigilant, stay verified, and stay safe.





